Competition document: The Invisible Battlespace
Updated 4 September 2018
1. Introduction
This Defence and Security Accelerator (DASA) competition is seeking proposals for novel and innovative technologies and approaches to enable UK Defence to effectively conduct electromagnetic (EM) operations across the air, land (urban and rural), sea, space and cyber domains.
The following broad question is posed: ‘How can UK Defence take a radically different approach to conducting operations effectively across or within an EM environment that is increasingly congested and contested?’
This competition has an initial £1 million to fund multiple proposals at Technology Readiness Level (TRL) 2 to 4. Additional funding is provisionally available for further phases of this competition to develop the technology to a higher TRL.
The competition closes at midday on Monday 22 October 2018.
2. Competition scope
2.1 Background
The EM spectrum is a critical resource used across the full range of UK defence and security operations. It is essential for communication, situational awareness, gaining information superiority, retaining full use of military and security capability and enabling joint effects in different defence and security domains. (In Defence, such resources are often referred to as ‘force multipliers’, reflecting their importance).
New and innovative approaches are needed to ensure UK defence and security personnel can continue to use the EM spectrum to full advantage and are not disadvantaged when operating in the EM environment as it becomes increasingly congested and contested.
The challenge for UK Defence to use the EM spectrum most effectively arises primarily from spectrum congestion, poor spectrum management, the environment and the impact of intentional disruption, principally from adversary electronic warfare (EW) capabilities. EW is military action that exploits EM energy to provide situational awareness and achieve offensive and defensive effects.
With the ever increasing demands placed upon the EM environment there is, more than ever, a requirement for UK defence and security personnel to have capability to be able to dynamically sense, understand, obscure, communicate, manage and effectively conduct dynamic offensive and defensive EM operations.
Military capabilities operating in the future multi-domain battlespace will need to function in a coherent and coordinated manner within the EM environment. Solutions which enable this are of significant interest and the opportunity for integration across the domains (stated in the introduction above) should be highlighted where appropriate.
2.2 Scope
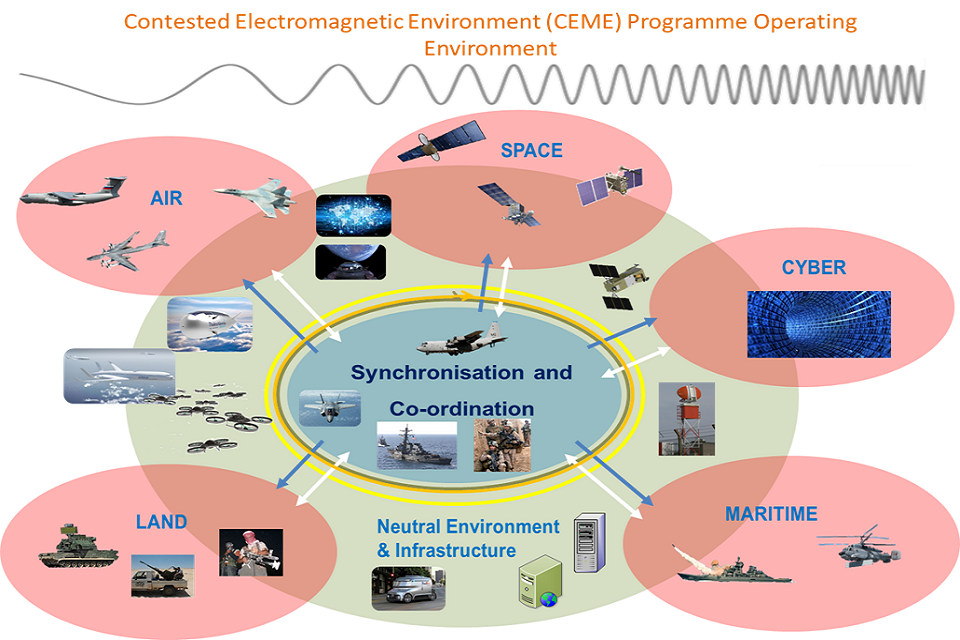
Figure 1 illustrates the EM operating environment for Defence. The inner ring depicts friendly forces, the middle ring acknowledges civilian non-combatants (civilians who are not taking a direct part in hostilities) and infrastructure, and the outer elements represent the adversary domains. The whole of this operating environment is in scope for this competition.
The EM spectrum covers all radio waves (for example, commercial radio and television, microwaves and radar), infrared radiation, visible light, ultraviolet radiation, X-rays and gamma rays. Factors influencing the EM spectrum include terrain, climate, solar activity and propagation media.
EM operations are all operations that enable, shape or exploit effective military activities within the EM environment (it is a force multiplier within the full spectrum of defence operations). EM operations include, or contribute to, (but are not limited to):
- EW (encompassing electronic attack, electronic defence and electronic surveillance)
- signals intelligence (SIGINT)
- electronic intelligence (ELINT)
- intelligence, surveillance, target acquisition and reconnaissance (ISTAR)
- navigation warfare (NAVWAR)
- battlespace spectrum management (BSM)
- communications, command and control (C2)
- cyber
2.3 Challenges
This competition is divided into 4 challenges which are described in more detail in the Challenge section below.
Challenges 1 and 2 are broad and look at understanding the EM environment, including how best to facilitate understanding, visualising, operating and conducting EW within a contested and congested EM environment.
Challenges 3 and 4 are more specific and focus on understanding how UK Defence could address adversary air defence systems within the EM environment. It is recognised that there is potential to consider the whole system to identify a wide range of potential solutions.
Whilst we are looking for ideas from across the EM spectrum (for example, electro-optical and infrared in the context of EW), the primary focus is within the radio and microwave bands. Concepts and ideas that look to utilise unconventional parts of the EM spectrum to address the challenges are also encouraged (for instance, an optical based solution to replace very high frequency (VHF) line-of-sight communication).
3. Competition challenges
Whilst we invite proposals that address any aspect of the broad question presented in the introduction above, we would encourage suppliers to focus proposals on one of the following four specific challenges.
For all of these challenges we are interested in proposals that consider a systems approach, including the potential to integrate with other existing, planned or potential future EM capabilities. Whilst the whole solution is not expected within Phase 1, the proposal could offer part of, or be an important step towards, a greater integrated solution to the challenge further into the future.
3.1 Challenge 1: Find me a channel
“We want to know what EM signals are out there, what equipment is generating them, what frequency bands they are using, how things are changing over time and how we make the best use of our equipment in the presence of all these signals’’
This challenge seeks innovative proposals to improve how UK Defence can sense, manage, visualise and utilise the EM spectrum (in real-time). This should include an understanding of the impact on our systems and operations, our adversaries’ actions, and non-combatants’ use of the EM spectrum.
Ideas must contribute to EM spectrum management processes and be able to contribute to sensing, identifying and visualising the positions of a variety EM emitters across the EM spectrum. This should include UK force emissions and EM signatures, as well as those of adversaries and civilians (including radars, radios, jammers, radio controlled improvised explosive devices and man-made noise). The operation of own force EM equipment and infrastructure should be able to be dynamically deconflicted across the EM spectrum, geographical battlespace, time and cyberspace in order to reduce conflicts and enable freedom of action.
Proposals addressing any aspects of the challenge will be considered. Particular areas of interest include, but are not limited to:
- dynamic, real time, full spectrum situational awareness
- understanding and visualising our own, adversary and civilian electromagnetic emissions
- techniques for electronic surveillance (for example, detect, separate, identify, locate and track emissions)
- ability to enhance electronic surveillance by fusing with or utilising other sensor sources
- electronic surveillance capabilities with sufficient fidelity to cue and trigger electronic attack or cyber effects
- electronic systems with reduced reliance on position, navigation and timing (for example, relative referencing and opportunistic calibration)
- advanced EM operations battlespace management aids (for example, real-time models and simulation and analysis for situational awareness and decision making)
- automatic translation of user needs to dynamic sensor tasking cognisant of a wide range of live operational factors
- autonomous dynamic spectrum access systems for resilience, stealth and reducing spectrum conflicts
- solutions to understand, identify and auto-allocate EM spectrum
- solutions to permit coordinated and synchronised tasking of EM operations
3.2 Challenge 2: Stay in contact
“We want to be able to communicate and share information with each other continuously when the EM environment is busy. We want to stop people interfering with our systems, interfere with their systems to make their life harder and disguise ourselves in the EM environment if we need to.’’
This challenge seeks innovative proposals to address how UK Defence can survive and conduct effective EW operations within an environment of multiple target/threat signals, multiple jammers and multiple radio systems, enabling us to operate and maintain capability effectively within the EM environment.
The key enablers to conducting effective EM operations are based primarily on combinations of:
The task (military requirement):
- sense
- intercept
- identify
- locate
- deceive
- jam
- inhibit
- neutralise
- stimulate
- protect
and the purpose (military objective):
- shared situational awareness
- indication and warning
- denial
- deception
- disruption
- degradation
- neutralisation
- destruction
- protection
For example, a combination of sensing, interception, identification and location are required to provide shared situational awareness.
Proposals addressing any aspects of the challenge will be considered. Particular areas of interest include, but are not limited to:
- unhindered, secure, reliable, capable command and control (from the highest echelons down to individuals)
- data management and efficient information dissemination
- networking across domains (joint force)
- electronic protection measures
- cognitive systems to access the spectrum, autonomously counter threats and allow rapid/continued operations against agile adversaries
- multi-function, multi-spectrum, agile, distributed, high dynamic range, wide/multi band, real-time EW systems
- technology transfer opportunities enabling operations within a congested EM environment
- EM stealth and camouflage to prevent adversaries finding, fixing, exploiting or understanding our emissions or true intent.
- EM signature management
- tools to visualise and develop courses of action using modelling and simulation
- tools to analyse and display success and impact on EW EM operations
3.3 Challenge 3: No use hiding from me
“We want to find ways to overcome attempts by our enemy to avoid detection as we go about trying to find and target them”
This challenge seeks innovative proposals to help UK Defence to conduct effective operations against modern Integrated Air Defence Systems (IADS) that may be employed by potential adversaries. This includes the ability to conduct intelligence, surveillance and reconnaissance of enemy IADS in order to locate all potential targets and threats.
Such air defences are expected to make use of a number of approaches to frustrate our efforts to do this. In particular, efforts will be taken to counter our ability to target systems of interest and to hide key equipment. In order to be effective against IADS, UK Defence requires a detailed understanding of potential technologies or process-based counters to these evasive approaches which include, but are not limited to:
- use of ‘low probability of intercept’ radar signals
- use of passive detection means
- off-site cueing through shared data and networks
- ability for engagement units to remain radar silent until very late in an engagement
- use of active missile sensors that reduce the amount of radio frequency emissions required for the support of weapons during an engagement
- emergent use of multi-spectral sensors on weapons (such as electro-optical and radar sensors combined)
Proposals addressing any aspect of the challenge will be considered. Particular areas of interest include, but are not limited to:
- methods to expose those IADS components that are hard to detect, such as radars, radio frequency communications networks, datalinks and unintentional emissions (approaches may include provoking the system to act in a way so as to be detectable by other equipment or assets)
- approaches to improve awareness of the location of IADS components and to map command and control chains though the use of the EM environment
- approaches to improve awareness of the adversary ‘Order of Battle’ (how and where the adversary capabilities are deployed) and command and control chains using the EM environments
- novel EM based concepts and effects that may disrupt, confuse or degrade IADS capabilities
3.4 Challenge 4: Taxi!
‘’We want to know how best to transport our effect delivery options into areas where there will be many EM ‘bad guy’ sensors looking at us, to deliver our effect on target.’’
Novel delivery mechanisms are sought which are capable of supporting effects at long range (target is between 250 and 450 km from the launch site) and long endurance (application of effect for between 30 and 90 minutes). The speed at which the effect may be delivered is also a factor as militarily useful systems will need to be able to fit within standard planning cycles. They may also have to keep pace with other support assets such as tactical aircraft. In addition, delivery mechanisms may have to contend with adverse meteorological conditions, a contested EM environment and varying geographical and topographical factors.
Proposals should consider the benefits, technical issues and likely technical risks associated with the following:
- size, weight and power demands of the payload that the proposed solution is expected to support
- likely unit cost drivers and, where possible, how mitigating factors such as the scale of purchase may impact final unit costs
- for platform based solutions, the on board vehicle system requirements and the effects of inclusion or exclusion on the design capabilities (for example navigation, data links, provision of power to a payload)
- survivability of the delivery mechanism
- factors that affect the ‘shelf-life’ of a delivery mechanism, for example, technical and cost impacts from developing ‘containerised’ systems requiring limited if any maintenance as opposed to those that require routine servicing
- tactical implications of the proposed speed of delivery over the ranges discussed
3.5 Clarification of what we want
Proposals should address the following aspects:
- novel approaches or solutions to address the broad question or defined challenges stated
- potential for further development beyond this phase with a view to the eventual maturation into real-world technology-enabled solutions in the future
- a systems approach with consideration of integration with other capabilities
- demonstration of clear applicability within a joint military operating environment
- proof-of-concept demonstration
- initial consideration of verification and validation options for the proposed solution
- consideration of what enabling capabilities are required to support the proposed solution
- indication of through life costs for the mature capability
- consideration of system level operational ‘measures of effectiveness’
At the end of Phase 1, we require a tangible demonstration of the innovation, which could take the form of a working prototype, model, video or simulation. We want innovation – but that does not mean that proposals cannot use existing technology. Repurposing of current capabilities and commercial-off-the-shelf equipment into new, related applications may offer a potentially easy, swift path to capability development which may be highly desirable for military applications.
3.6 Clarification of what we do not want
For this competition we are not interested in proposals for:
- consultancy, paper-based studies or literature reviews
- solutions that do not offer significant benefit to Defence
- proposals that only offer a written report
- proposals that cannot demonstrate feasibility within the Phase 1 timescale
- identical resubmission of a previous bid to DASA or MOD without modification
- minor improvements on existing high TRL technologies (unless it being applied in a novel way to the challenge)
- proposals which offer no real long-term prospect of integration into defence capabilities
- proposals with no real prospect of out-competing existing technological solutions
4. Exploitation
It is important that over the lifetime of DASA competitions, ideas are accelerated towards appropriate end-users, to enhance capability. How long this takes will be dependent on the nature and starting point of the innovation. Early identification and appropriate engagement with potential users during the competition and subsequent phases is essential.
All proposals to DASA should articulate the development in TRL of the output over the lifetime of the contract and how this relates to improved operational capability. For this competition it is envisaged that proposals will start at a minimum of TRL 2, though higher TRL applications will be welcome (up to TRL 4).
The deliverables in your proposal (especially the final demonstration) should be designed to provide evidence that you are going to / have reached the intended TRL by the end of the contract. The final demonstration should evidence that full development of the solution would indeed provide improved operational capability to the user.
Subsequent phases will focus on TRL >2. The evidence generated during Phase 1 should support the development of the business case for Phase 2, with the aim of making it as easy as possible for potential collaborators to identify the innovative elements of your proposal in order to consider routes for exploitation.
It is important right from the start that DASA and end-users understand how your idea will deliver longer term improvements to defence capability and how it could be integrated with other relevant capabilities. Therefore, you may wish to include some of the following information, where known, to help the assessors understand your exploitation plans:
- the intended defence users of your final product and whether you have engaged with the end-users or their procurement organisation
- the current TRL of the innovation and where you realistically think it will be by the end of this phase
- awareness of, and alignment to, any existing end-user procurement programmes
- the benefits (for example, in cost, time, improved capability) that your solution will provide to the user
- whether it is likely to be a standalone product or integrated with other technologies or platforms
- expected additional work required beyond the end of the contract to develop an operationally deployable commercial product (for example, ‘scaling up’ for manufacture, cyber security, integration with existing technologies, environmental operating conditions)
- additional future applications and markets for exploitation
- wider collaborations and networks you have already developed or any additional relationships you see as a requirement to support exploitation
- requirements for access to external assets, including Government Furnished Assets, Equipment and Information (GFX), for example, data, equipment, materials and facilities
- how you intend to demonstrate the outputs at the end of this phase, what form the demonstration would take and whether it will require any special facilities (for example, outdoor space, specific venue)
- how your product could be tested in a representative environment in later phases
- any specific legal, commercial or regulatory considerations for exploitation
5. How to apply
Proposals for funding to meet these challenges must be submitted by midday on 22 October 2018 via the DASA submission service for which you will be required to register.
The initial funding of £1 million is expected to fund at least 10 proposals. Proposals must be less than £100k cost to DASA (although you may choose to use additional funds from elsewhere to meet the challenge). We recommend that suppliers place their applications in the range of £50k to £100k. If successful, Phase 1 contracts will be awarded for a duration of 6 months.
Additional funding for subsequent phases to increase TRL further towards exploitation is anticipated to be available. Any further phases will be open to applications from all suppliers and not just those that submitted Phase 1 successful bids.
Further guidance on submitting a proposal is available on the DASA website.
5.1 What your proposal must include
When submitting a proposal, you must complete all sections of the online form, including an appropriate level of technical information to allow assessment of the bid and a completed finances section.
A project plan with clear milestones and deliverables must also be provided. Deliverables must be well defined and designed to provide evidence of progress against the project plan and the end-point for this phase.
The proposal should focus on this phase but should also include a brief outline of the next stages of work required for exploitation.
Identification of any ethical/legal/regulatory factors within your proposal and how the associated risks will be managed, including break points in the project if approvals are not received, must be included. Further details are available in the DASA ethical, legal and regulatory guidance.
In addition, requirements for access to Government Furnished Assets or Information (GFX) should be included in your proposal with information on availability and costs.
Completed proposals must comply with the financial limit for this competition which has an upper limit of £100k per proposal. Applications will be rejected if the financial cost exceeds this capped level.
Proposals must include costed participation at the following two DASA events:
- a collaboration event
- a demonstration event
Both events will be held in the UK.
5.2 Public facing information
A brief abstract will be requested if the proposal is funded. This will be used by DASA and other government departments as appropriate, to describe the project and its intended outcomes and benefits. It will be used at DASA events in relation to this competition and placed on the DASA website, along with your company information and generic contact details.
5.3 How your proposal will be assessed
All proposals will undergo an initial sift and if the application does not meet certain minimum standards (for example funding limits) it will not be taken forward to full assessment.
Proposals will then be assessed against the standard DASA assessment criteria by subject matter experts from the MOD (including Dstl), other government departments and front-line military commands. On occasion, where expertise may not exist within the Civil Service, we may use external academic review under a non-disclosure agreement. Suppliers will not have the opportunity to comment on assessors comments.
Further guidance on how your proposal is assessed is available on the DASA website.
After assessment, proposals will be discussed internally at a Decision Conference where, based on the assessments, budget and wider strategic considerations, a decision will be made on the proposals that are recommended for funding.
Proposals that are unsuccessful will receive brief feedback after the Decision Conference.
5.4 Things you should know about DASA contracts
Please read the DASA terms and conditions which contains important information for suppliers. For this competition we will be using the Short Form Contract (SFC).
Funded projects will be allocated a Technical Partner as a technical point of contact. In addition, the DASA team will work with you to support delivery and exploitation.
Deliverables from DASA contracts will be made available to MOD, front-line commands, and may be subject to review by relevant government departments.
The full-rights outputs of funded work may be exposed to international government partners. This is to promote international collaboration and to give projects the best chance of exploitation through exposure to a larger scope of requirements. This will only be done under the protection of existing inter-governmental memoranda of understanding.
6. Phase 1 dates
| Competition open | Thursday 23 August 2018 |
| Dial in | Tuesday 11 September 2018 |
| Pre bookable 1-1 telecom sessions | Tuesday 11 September 2018 and Wednesday 12 September 2018 |
| Competition closes | Monday 22 October at midday |
| Decision conference | by Friday 16 November 2018 |
| Contracting | by Friday 30 November 2018 |
6.1 Supporting events
- Tuesday 11 September 2018 (morning) – A dial-in session providing further detail on the problem space and a chance to ask questions in an open forum. If you would like to participate, please register on the Eventbrite page.
- Tuesday 11 September 2018 (afternoon) – A series of 20 minute one-to-one teleconference sessions, giving you the opportunity to ask specific questions. If you would like to participate, please register on the Eventbrite page.
- Wednesday 12 September 2018 (morning) – An additional series of 20 minute one-to-one teleconference sessions, giving you the opportunity to ask specific questions. If you would like to participate, please register on the Eventbrite page.
7. Help
Competition queries including on process, application, technical, commercial and intellectual property aspects should be sent to [email protected], quoting the competition title. While all reasonable efforts will be made to answer queries, DASA reserves the right to impose management controls if volumes of queries restrict fair access of information to all potential suppliers
